Behind every company, local authority, or government agency lies a complex network of partners, both a driver of productivity and a source of potential risks. At the heart of risk management, assessing the integrity of these third parties enables the identification, understanding, and anticipation of these external threats. Far more than an administrative constraint, it is a strategic decision-making tool. Its effectiveness is the key to a robust and appropriate risk management plan.
But how can you ensure the reliability of third-party assessment? Discover the methodological approaches to build a sustainable and effective assessment framework, serving the compliance and accountability of your company, local authority, or government agency.

Several third-party assessment approaches can be combined depending on the identified risk level and the company’s, local authority’s, or government agency’s willingness to deepen its assessment process.
Documentary and declarative analysis consists of gathering information directly from the third parties with which it maintains relationships, through standardized questionnaires, compliance forms, and review of legal and administrative documents.
This approach allows for the creation of an initial database. However, it has a limitation: it relies solely on third-party declarations, which may be incomplete, inaccurate, or biased.
Due diligence consists of cross-checking, verifying, and enriching the information provided by third parties using independent and reliable external sources (public databases, financial statements, press and specialized publications, rating agency reports, etc.).
This approach reveals potential weak signals, such as a third party’s past involvement in an international corruption case, financial fragility, opaque relationships with high-risk entities, or environmental violations.
More rigorous, the risk-based approach calibrates the level of vigilance to the risk level, based on objective criteria:
By concentrating resources on the most sensitive third parties, this method avoids complex, costly assessment procedures that are unsuitable for low-risk third parties.
To be effective, third-party integrity assessment requires a structured, methodical, and rigorous six-step approach.

Evaluating third parties begins with an identification and inventory phase. It includes:


Once third parties are inventoried, the company, local authority, or government agency collects information. Depending on the chosen approach, data comes from various internal and external sources:


Not all third parties present the same level of risk. Following the initial information collection, the company, local authority, or government agency analyzes the relevance of a more in-depth analysis.
Certain weak signals may justify closer examination. While not necessarily disqualifying, a past corruption scandal, relationships with the public sector, or an opaque legal structure are all "red flags" that call for vigilance.
💡Based on artificial intelligence, the solution developed by Values Associates automates and accelerates information collection and enables assessment of whether to deepen the evaluation using a screening tool.


Analysis begins after information collection. The objective is to assess, for each third party, the nature and criticality of the risks to which it exposes the organization.
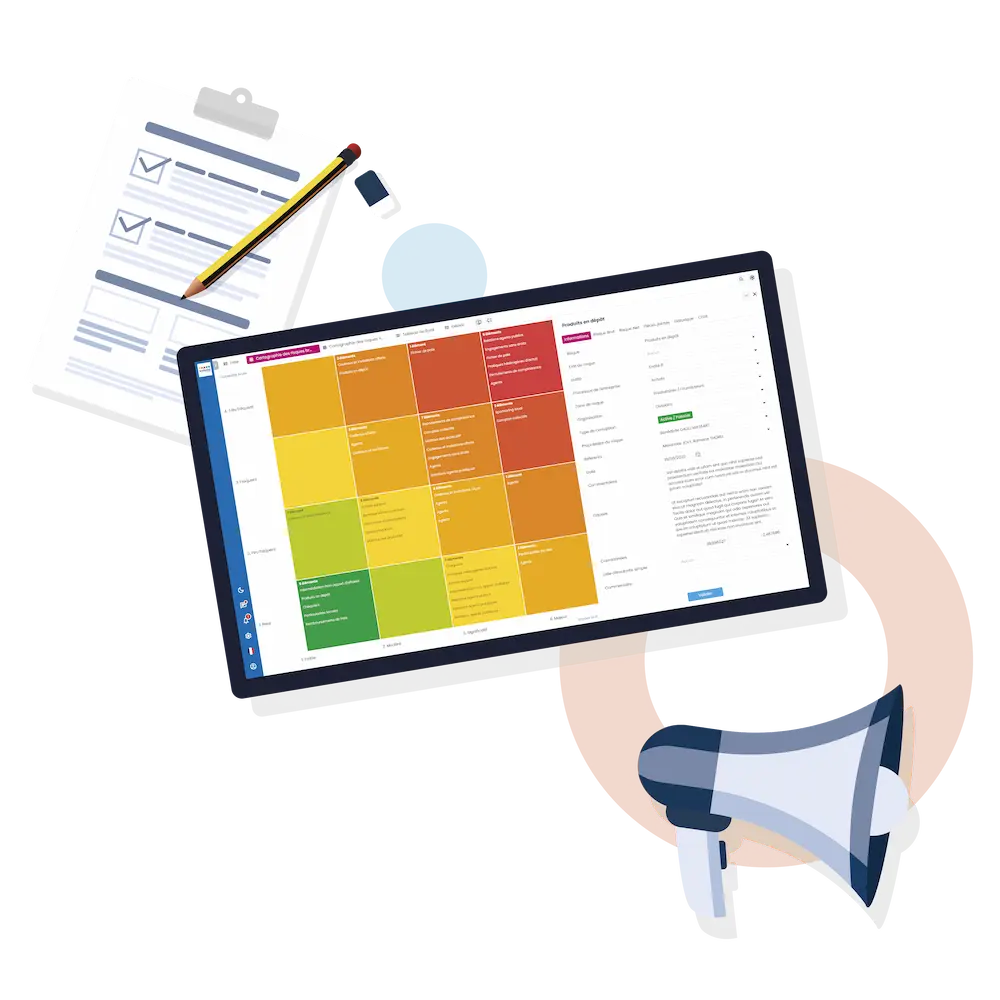
The scoring method consists of assigning scores on an evaluation scale based on objective criteria defined in advance. The organization notably cross-references the probability of risk occurrence with their potential severity. Criteria vary depending on organizations. Companies, local authorities, and government agencies do not share the same priorities. Nor do they have the same risk tolerance capacity.
Scoring classifies third parties according to their risk level. Decisions are arbitrated and validated through automatic criteria or a manual approval procedure (hierarchical circuit, validation committee).


Faced with each risk, the company, local authority, or government agency decides on the action to take. It has 5 options:
Concrete prevention, mitigation, and remediation measures are numerous and varied. They can include systematic due diligence procedures, strengthened financial or IT controls, redefinition of contractual clauses, implementation of training programs, or termination of a high-risk partnership.


The risk associated with a third party is never static. A change in governance, a judicial sanction, corruption of an agent, or a major cyberattack can radically transform a third party's risk profile.
This is why third-party assessment must be an ongoing process, with periodic controls, regular audits, regular database updates, external monitoring, and official alerts.
This dynamic approach enables adaptation of third-party integrity assessment to risk volatility and maintains an accurate and up-to-date risk map.

Several best practices and tools determine the effectiveness, usefulness, and reliability of the third-party assessment framework and ensure compliance with the recommendations of the French Anti-Corruption Agency (AFA).
To be reliable, third-party assessment must be based on accurate and up-to-date information. Incomplete or outdated data can mask a critical risk. This is the case, for example, if a company, local authority, or government agency continues to work with a supplier registered as solvent, without taking into account its recent financial deterioration.
Information quality and integrity are ensured through rigorous data collection, multiple sources, and regular updates.
Another pitfall lies in the subjectivity of analyses. Customizing third-party assessment criteria by department makes results inconsistent, heterogeneous, and difficult to use across the organization.
Adopting a common analytical framework avoids individual biases, harmonizes decisions, and strengthens the legitimacy of the process. It must be based on objective and measurable criteria and be collectively validated to ensure buy-in from all stakeholders.
Historically, third-party assessment relied on manual controls and Excel files. Given the volume and diversity of data, this approach quickly becomes time-consuming, costly, error-prone, and ineffective.
Specialized digital solutions make the third-party assessment process more reliable and secure. Through their functionalities, companies, local authorities, and government agencies can automate information collection, perform intelligent third-party screening, centralize data, automatically calculate risk scores, integrate alerts, and monitor action plans in real time.
Software also ensures complete documentation and traceability of information and processes, facilitating audits and demonstrating compliance during inspections.
Third-party assessment is far more than a compliance exercise: it is a strategic pillar of risk management and a key factor in sustainable performance. It enables companies, local authorities, and government agencies to secure their relationships while meeting growing demands for transparency and accountability.
However, its effectiveness relies on a delicate balance between methodological rigor, reliable data, objective criteria, and high-performance digital tools. When it is dynamic, structured, and shared, the third-party assessment approach becomes a true competitive advantage.
100% intuitive and secure, the third-party assessment software developed by Values Associates offers a fully customized and high-performance approach to third-party assessment.
Built on Mistral’s French models, our AI solution optimizes risk detection and drastically reduces analysis and synthesis time.