Companies, local authorities, and government agencies operate within an interconnected network of external partners. Each represents both an opportunity and a vulnerability. In this complex context, third-party assessment has become a cornerstone of risk management.
However, not all third parties present the same level of threat. Some are critical to business continuity; others expose the organization to legal, reputational, or financial risks. Therefore, classifying and prioritizing third-party risks is a strategic and structural decision.
Analyze and combine classification methods and criteria for external risks to achieve a tailored, effective, and proportionate third-party assessment.

The third parties of a company, local authority, or government agency present highly diverse profiles. Classifying these partners according to their type enables the third-party assessment framework to be adapted and customized.
The risks associated with third parties vary depending on their role. For example, a raw materials supplier does not present the same risk profile as a lobbyist consultant in a sensitive geopolitical area.
By classifying third parties by type, the company, local authority, or government agency can adjust its third-party assessment methods, particularly:
The third parties surrounding companies, local authorities, and government agencies present highly heterogeneous risk profiles. Their assessment will be more or less thorough depending on the organization’s priorities:

Another methodical approach consists of classifying third parties by risk nature. It enables third-party mapping to be adapted according to the priorities and vulnerabilities of the company, local authority, or government agency.
The robustness of companies, local authorities, and government agencies depends on several elements: the sector of activity, geographical location, regulatory obligations, budgetary resilience, or environmental requirements.
Having a detailed and segmented view by risk nature directs the third-party assessment framework toward the most critical activities for the organization.
The risks to which companies, local authorities, and government agencies are exposed are of diverse natures. Organizations’ vigilance will depend on their priorities and vulnerabilities.
For example, some will be more sensitive to economic risk and others to regulatory risk:
Financial strength and solvency of the third party are key criteria to ensure the ability to honor contractual commitments. Ratings and payment histories provide valuable indicators.
They refer to a third party’s ability to ensure consistent and reliable service delivery, even in the event of disruptions. Even if financially sound, a strategic third party in the value chain requires enhanced assessment to avoid any operational disruption.
They expose the company, local authority, or government agency to heavy financial and reputational penalties. Third-party assessment focuses on the absence of sanctions, compliance with laws and regulations, or the third party’s legal history.
ESG criteria are now at the center of stakeholder concerns. Third-party assessment verifies respect for human rights throughout the supply chain, environmental commitment, or governance ethics.
Third parties are critical entry points for cyberattacks, malicious intrusions, data theft, or operational disruptions. Third-party assessment focuses on the third party’s IT maturity, the sensitivity of data exchanged, or business continuity capability.
The location of the third party in a high-risk area, with strict legislation, or under international surveillance requires enhanced assessment and control measures.
The public sector and the private sector have specific logics and constraints that influence the risk profile. For example, third parties involved in public procurement are subject to strong transparency and fairness requirements. In the private sector, finance or healthcare respond to strict laws and regulations.

Classifying third parties by risk level is a widely used third-party assessment practice. It enables companies, local authorities, and government agencies to target their efforts on the most critical partners and threats.
Not all third parties require the same degree of vigilance. Classification by risk level helps to proportion the third-party assessment framework and to direct resources toward the most critical issues, in line with the recommendations of the French Anti-Corruption Agency (AFA).
Thus, for a low-risk third party, simplified periodic verifications will suffice. In contrast, a high-risk third party will require sustained vigilance with the implementation of frequent audits, automated due diligence, enhanced mitigation measures, and sometimes even contractual restrictions.

Risk levels are generally classified into three main categories:
Some advanced models add intermediate levels (extreme risks or residual risks).
Several approaches are used to assess and classify third parties according to their risk level:
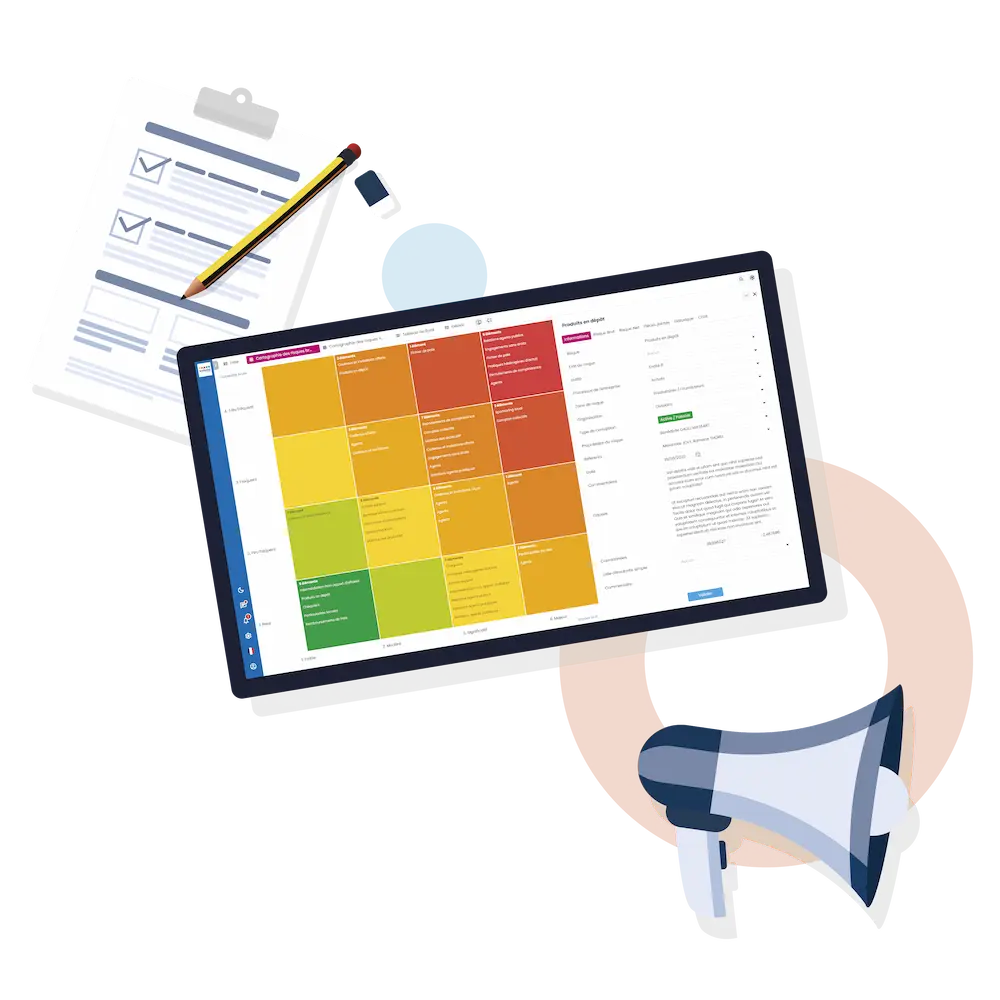
Once third parties are classified, the challenge is to successfully cross-reference this data effectively to derive concrete decisions. Digital solutions facilitate this complex process.
Depending on their functionalities, third-party assessment software enables companies, local authorities, and government agencies to:

Type, risk nature, risk level: choosing the criteria for classifying third parties and associated risks is strategic.
Segmentation enables priorities to be ranked and assessment and control efforts to be targeted on the highest-risk third parties. The use of specialized digital solutions facilitates filtering and combining criteria for dynamic and proactive third-party assessment.
The third-party assessment software developed by Values Associates overcomes the limitations of screening tools often considered imperfect.
Using artificial intelligence, you obtain intelligent, clear, and sourced summaries, with segmentation of third parties and risks by customizable category. Based on models from the French company Mistral, our solution can be adapted to meet your specific business processes, and for example adjust the type of information sought.