Cybersecurity has become a central issue for all organizations, regardless of their size or sector of activity.
Cyber risks, or IT risks, refer to all threats likely to affect the security, availability, integrity, and confidentiality of information systems.
Faced with this increasing exposure to digital threats (cyberattacks, data leaks, system compromise), organizations must adopt a structured approach to risk identification, assessment, and monitoring to strengthen their digital resilience.

Cybersecurity risks are not limited to external attacks. They also cover internal flaws, human errors, organizational failures, or vulnerabilities related to third parties and service providers. Their impact can be financial, legal, operational, or reputational.
The main challenges are:
Clear information security governance forms the basis of effective cyber risk management.
Associated threats notably concern:
Controlling access rights is essential to limit the attack surface:
Technical security relies on prevention and resilience:
Suppliers and partners represent a major risk vector:
Preparation and responsiveness to incidents determine recovery capacity:
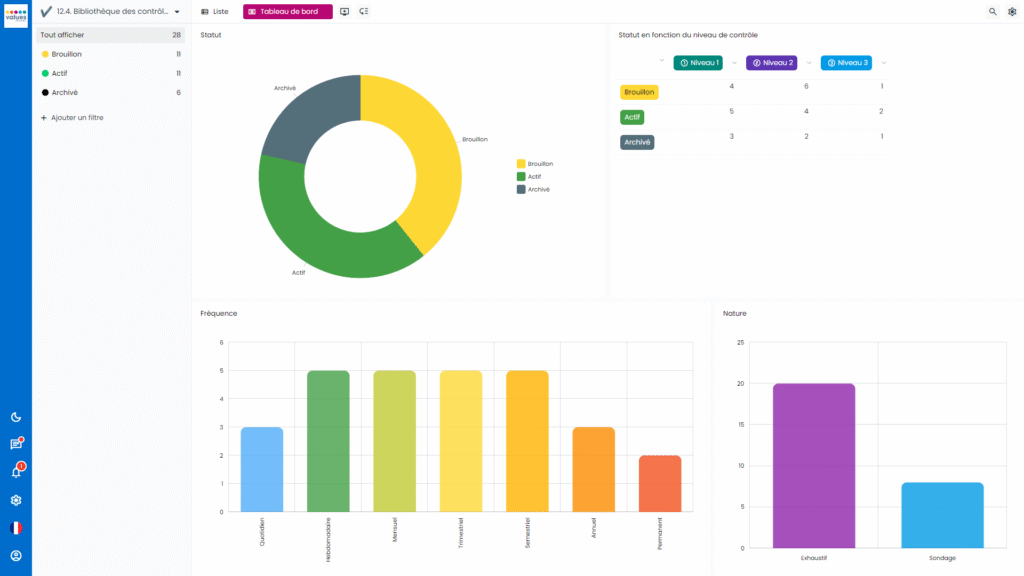
Our risk management software allows organizations to master their cyber and IT risks through an integrated approach to cybersecurity and compliance.
Centralize data and automate digital risk assessment
Produce reliable reports compliant with ISO 27001, DORA, NIS2, and GDPR frameworks
Facilitate collaboration between IT departments, compliance, and senior management
Cyber risks are governed by several frameworks and regulations, which set best practices and compliance requirements:
These frameworks provide a methodological basis for identifying, assessing, and reducing digital risks within organizations.

For effective management of cybersecurity risks, several levers can be activated:

Cyber risks are cross-functional and evolving. They concern technical infrastructure as much as internal processes and corporate culture.
Mastering them relies on a global approach combining governance, prevention, awareness, and compliance.
Adopting structured cyber and IT risk management makes it possible to sustainably strengthen the organization’s resilience and digital trust.
Values Associates risk management software is fully aligned with this logic: it helps organizations centralize their assessments, track their action plans, and accelerate compliance with cybersecurity requirements.
Cyber and IT risks encompass all threats likely to affect information systems: cyberattacks, data leaks, human errors, technical failures, or vulnerabilities related to external providers.
IT risks mainly concern technical aspects related to systems and data.
Cyber risks additionally encompass the organizational, regulatory, and human dimensions of digital security.
Organizations must comply with several frameworks: ISO 27001 / 27002, DORA, NIS2, GDPR, and ANSSI recommendations.
These frameworks set requirements for security, governance, and business continuity.
An effective approach relies on clear governance, awareness programs, rigorous technical monitoring (updates, backups, access controls), and regular assessment of cyber maturity.
Values Associates software allows you to centralize data, automate risk assessment, and produce reports compliant with regulatory frameworks.
It facilitates collaboration between IT, compliance, and senior management for sustainable digital security.